In a large campus network, you need to control which users can access which resources.
Traditional ACLs work, but they create a major scalability problem when your network grows.The IP-Based Segmentation Problem
Your network uses ACLs to control which devices can talk to which resources.
But traditional ACLs are based on IP addresses. When a device moves, gets a new IP, or when your network grows, you have to update every ACL on every switch.Imagine your campus network has three groups of users: Employees, Contractors, and Guests.
You want Employees to access the server VLAN, Contractors to reach only specific resources, and Guests to access only the Internet.With traditional ACLs, you write rules based on source and destination IP addresses.
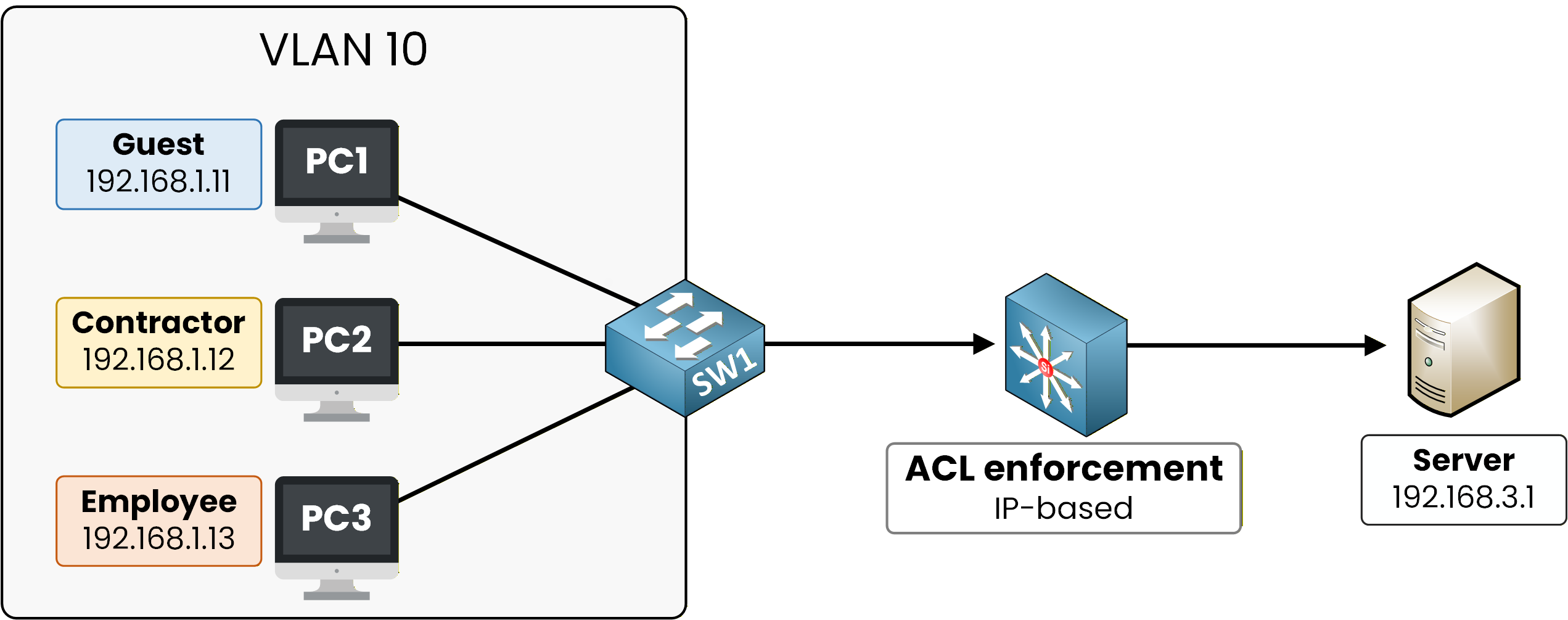
Figure 1 – IP-based ACLs work
This works as long as every user stays on the same subnet.
But what happens when an Employee moves to a different floor and gets a new IP address?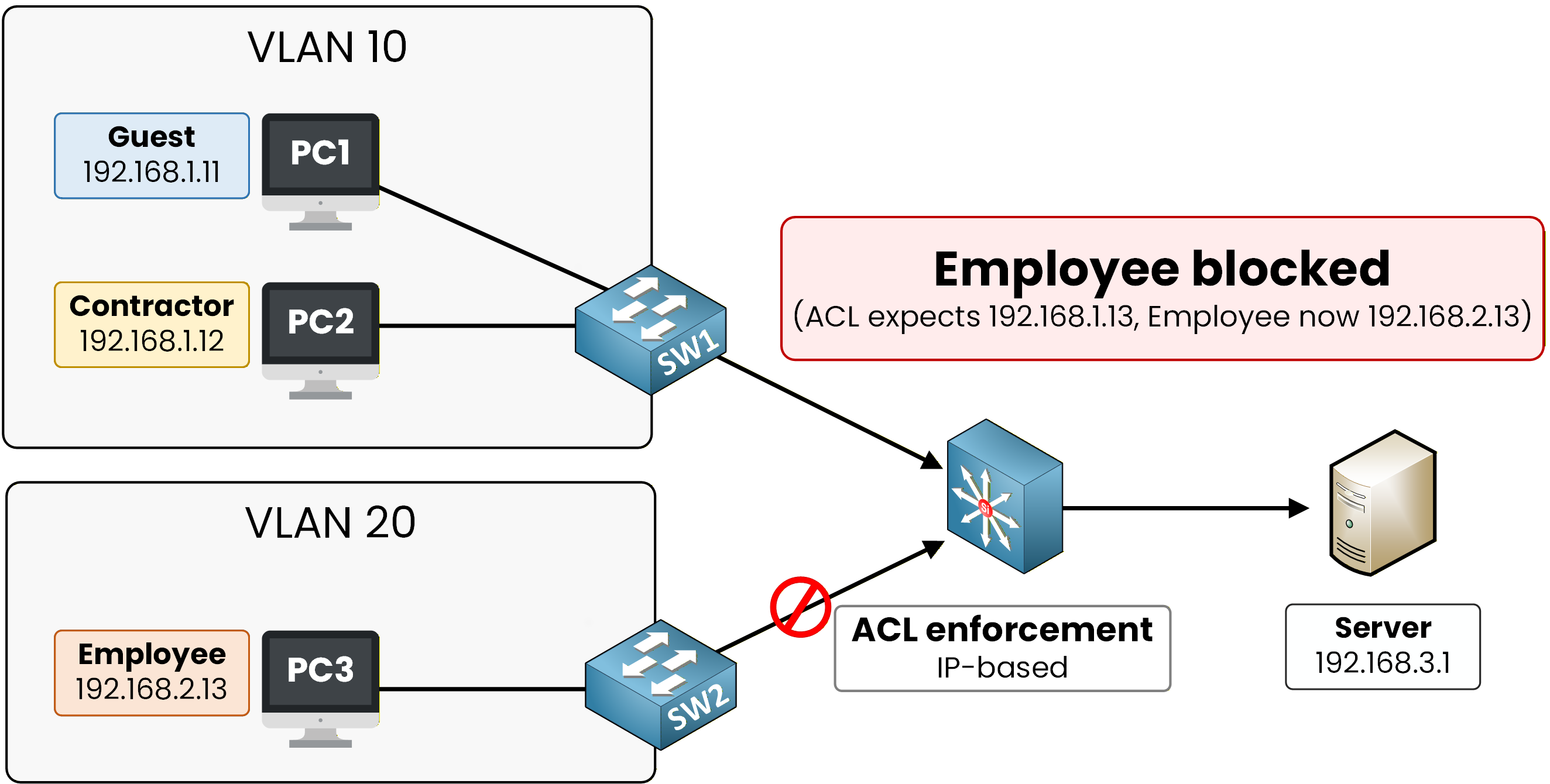
Figure 2 – Employee moved, ACL broken
Your ACLs no longer match. You have to update the rules manually.
This approach does not scale. In a large campus with hundreds of switches and thousands of users, maintaining IP-based ACLs across every device becomes unmanageable.Answer the question below
Traditional ACLs use which type of address to filter traffic?
TrustSec at a Glance
Cisco TrustSec takes a different approach.
Instead of filtering by IP address, TrustSec classifies users and devices by identity, not IP addresses.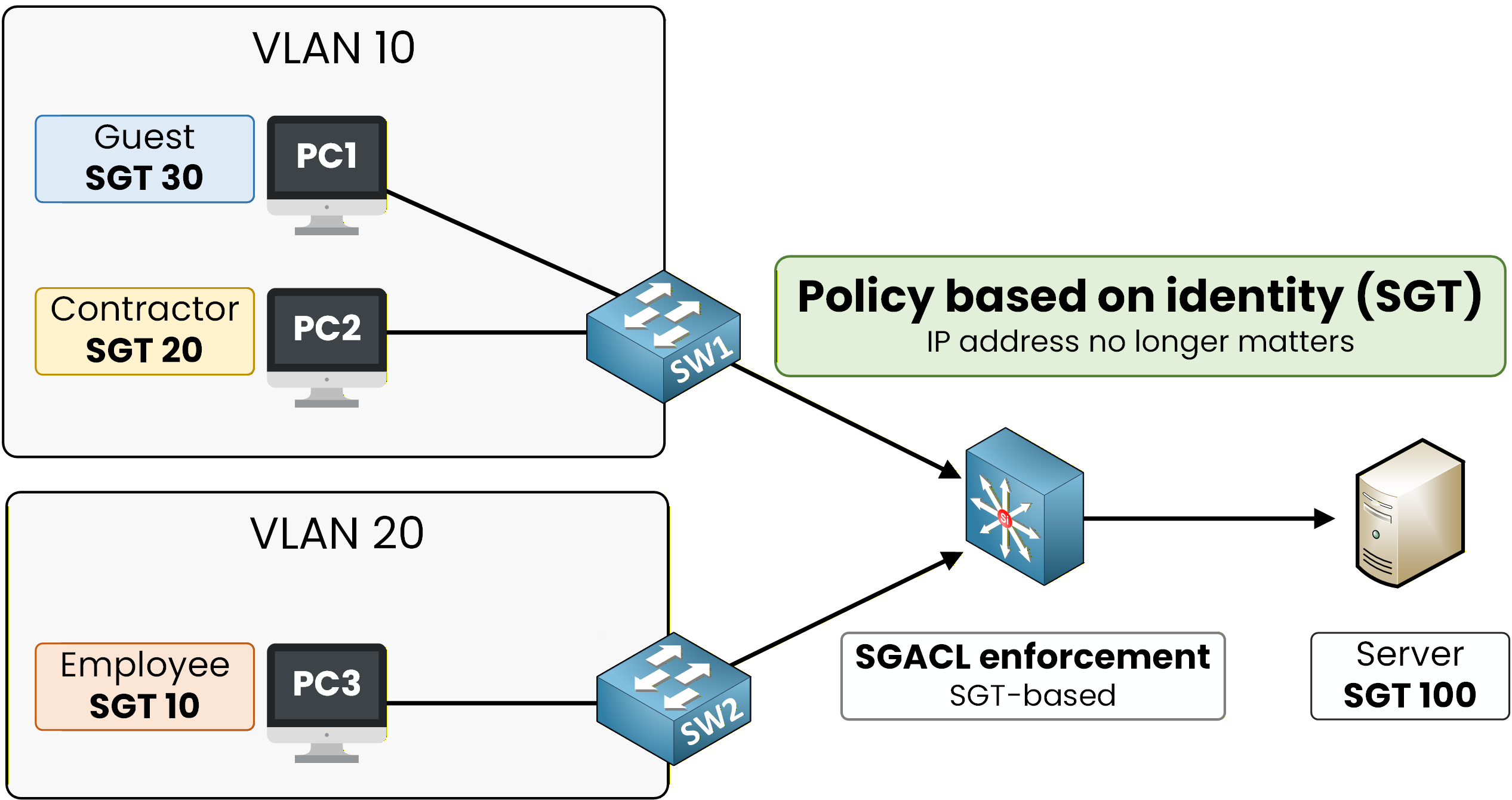
Figure 3 – SGT follows user identity
When a user connects to the network, your switch assigns a Security Group Tag (SGT) to their traffic.
This tag stays with the traffic as it crosses the network. It does not matter which port, VLAN, or subnet the user is on.Policies are then enforced based on the SGT, not the IP address.
If an Employee moves to a different floor, their SGT stays the same. No ACL changes needed.Answer the question below
Does TrustSec classify traffic based on IP addresses or identity?
You've seen the problem TrustSec solves. Now let's break down exactly how it works.
TrustSec operates in two main steps: first, your network assigns an SGT to each user based on their identity. Then, your network enforces security policies using these tags.Step 1: SGT Assignment
When a user authenticates to the network (typically through 802.1X), the RADIUS server (like Cisco ISE) returns an SGT value along with the authentication response.
40 % Complete: you’re making great progress
Unlock the rest of this lesson
If you’d like to continue your CCNA journey, simply create your free account.
Access all CCNA lessons
Practice with hands-on labs
Train with Practice exams and Quizzes
Progress tracking in your dashboard
Made by network engineers - CCNP certified
learners globally