Firewalls have been around for decades.
They inspect traffic between networks and decide what passes and what does not.
But the internet has changed. Modern applications and threats no longer fit the model a traditional firewall was built for.The Traditional Firewall
A traditional firewall filters traffic based on Layer 3 and Layer 4 information.
It looks at the source IP, the destination IP, the port number, and the protocol.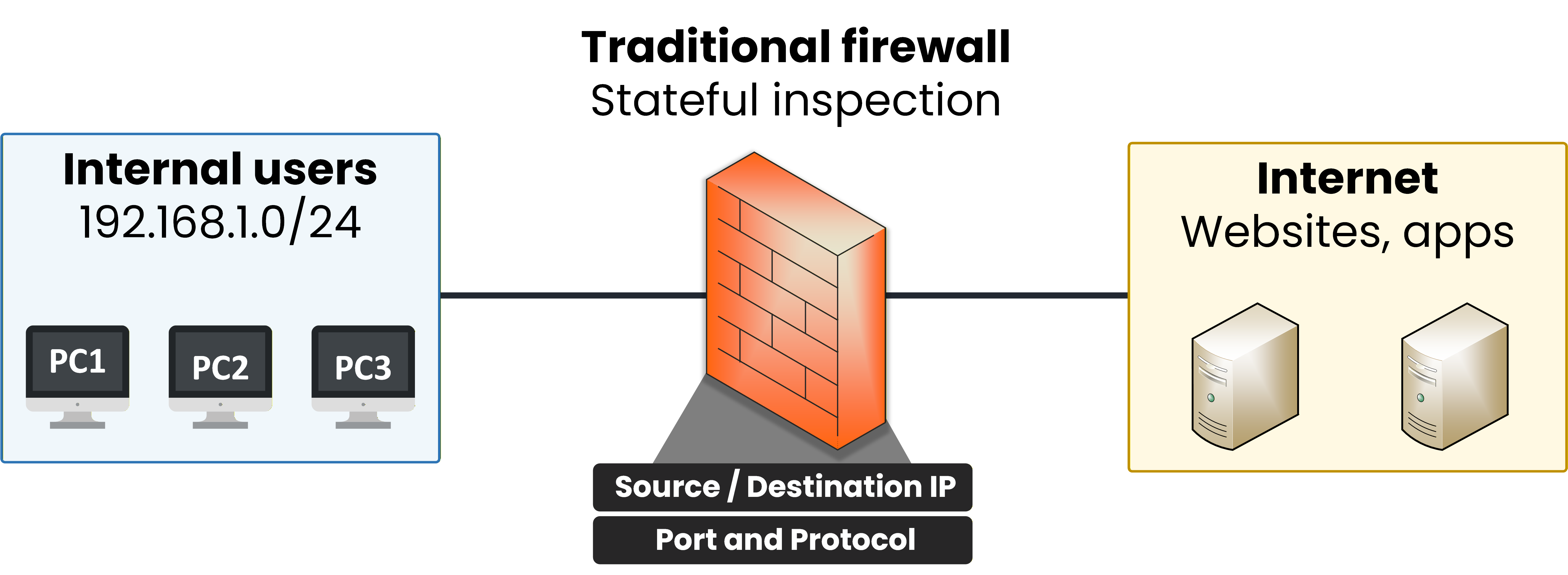
Figure 1 – Traditional firewall filters by IP and port
The firewall maintains a stateful session table to track connections.
It allows return traffic for established sessions and blocks anything outside its ruleset.This worked well when each application had its own well-known port.
Web traffic used port 80. Email used port 25. Telnet used port 23. You blocked a port, you blocked the app.Answer the question below
What type of session table does a traditional firewall use to track active connections?
The Modern Problem
Today, almost every application runs over HTTPS on TCP port 443.
Salesforce, Dropbox, Zoom, and even malware command-and-control channels all look identical to a traditional firewall.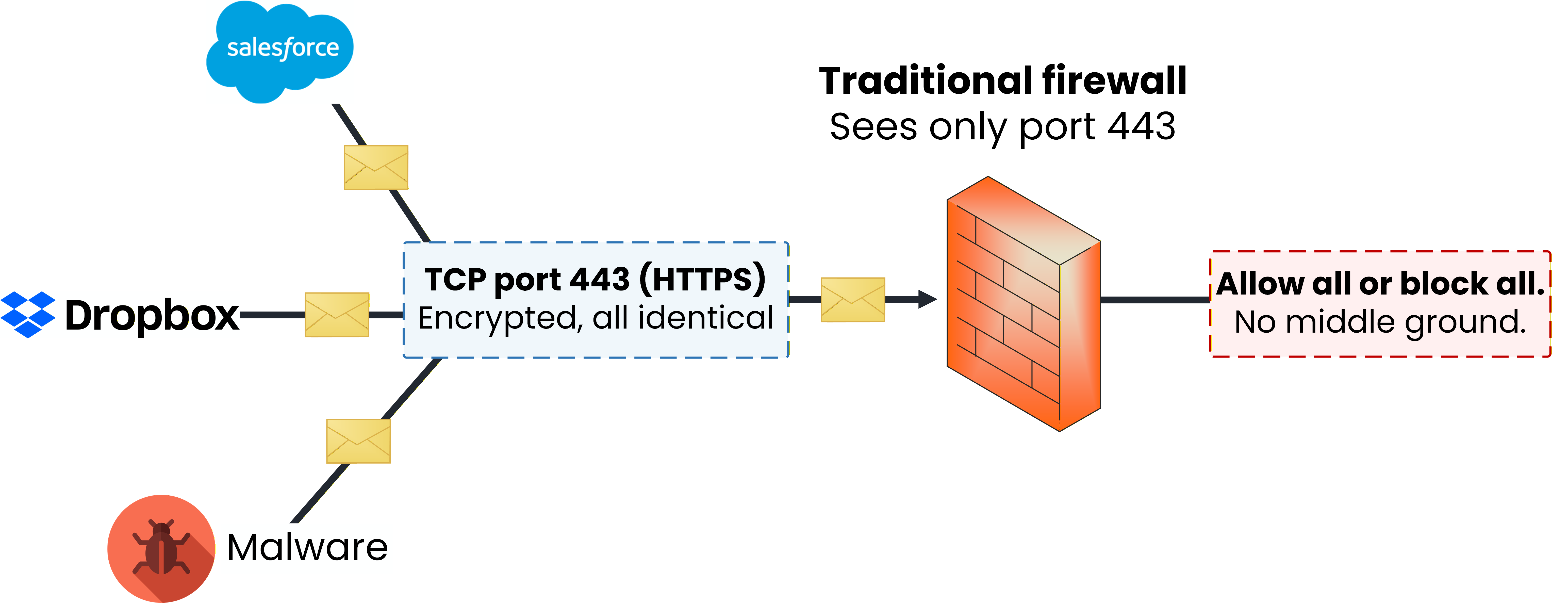
Figure 2 – Modern traffic hides many apps and threats inside port 443
The firewall has two choices: allow all port 443 traffic, or block it entirely.
Neither option is acceptable in a real enterprise.You need a firewall that sees inside the traffic, not just around it.
That is what a Next-Generation Firewall does.Answer the question below
What Layer does a traditional firewall inspect to make filtering decisions?
A Next-Generation Firewall (NGFW) goes far beyond port-based filtering.
Two capabilities define what makes a firewall "next-generation": application awareness and integrated intrusion prevention.40 % Complete: you’re making great progress
Unlock the rest of this lesson
If you’d like to continue your CCNA journey, simply create your free account.
Access all CCNA lessons
Practice with hands-on labs
Train with Practice exams and Quizzes
Progress tracking in your dashboard
Made by network engineers - CCNP certified
learners globally