In the previous lesson, you configured a site-to-site VPN using IPsec.
Traffic between the New York and San Francisco networks is now encrypted across the Internet.Why GRE over IPsec?
However, a limitation remains.
IPsec alone cannot transport dynamic routing protocols. You cannot run OSPF or EIGRP directly over a standalone IPsec tunnel because IPsec only protects unicast IP traffic.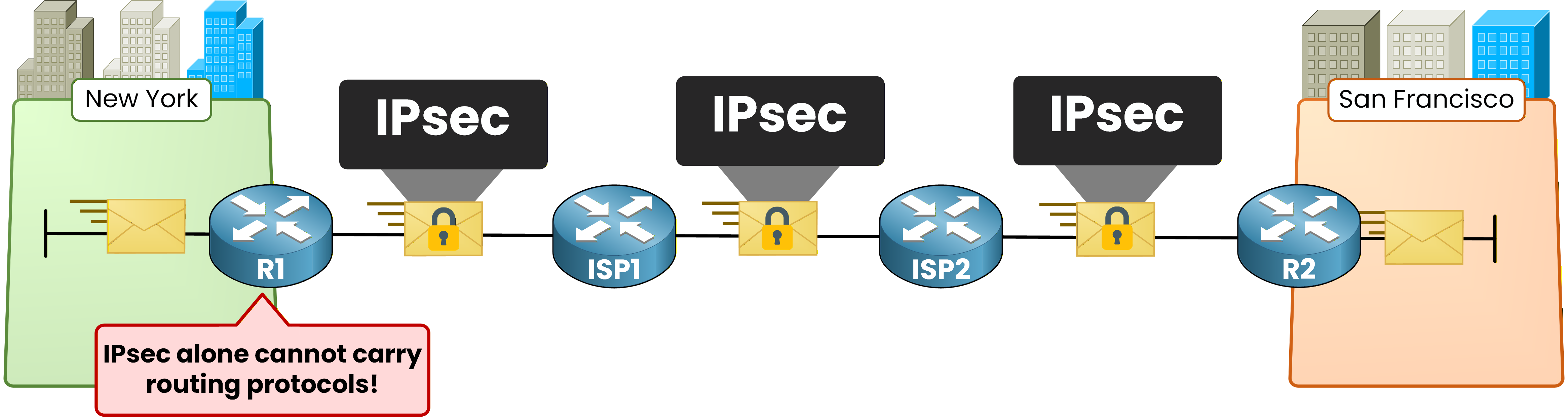
Figure 1 - IPsec cannot carry routing protocols
This limitation prevents routers from forming routing adjacencies directly through IPsec.
The answer is GRE over IPsec. You build a GRE tunnel first.
GRE can carry any traffic including multicast. Then you wrap that GRE tunnel inside IPsec to encrypt everything.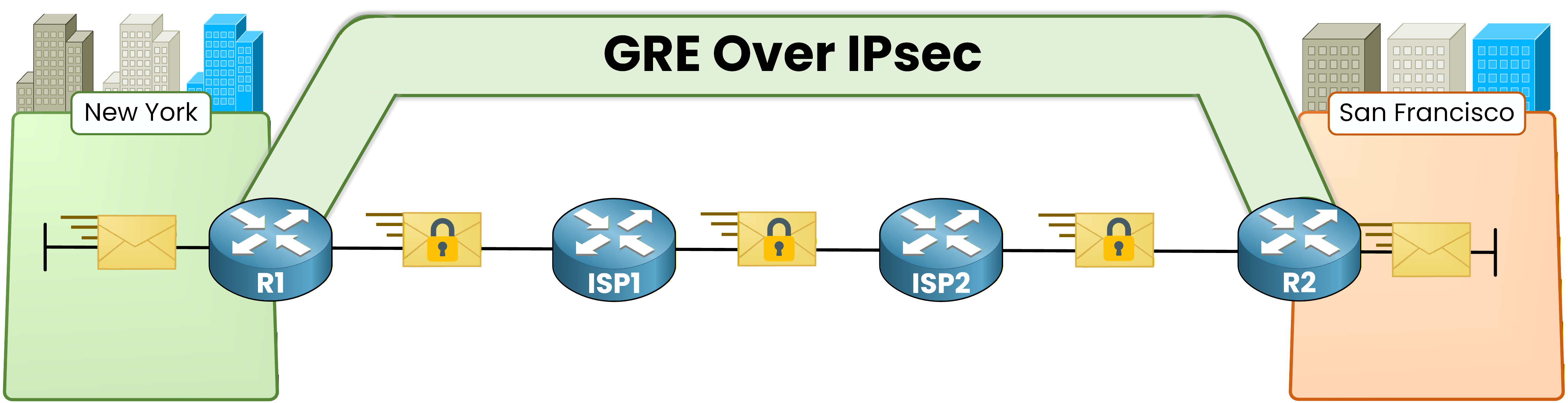
Figure 2 - GRE over IPsec topology
GRE provides the transport flexibility.
IPsec provides the encryption. Together they give you a secure overlay that supports dynamic routing.Answer the question below
What protocol allows routing protocols like OSPF to pass through an IPsec tunnel?
Why Transport Mode?
There is also a critical design choice: which IPsec mode do you use?
In the IPsec Fundamentals lesson, you used tunnel mode. It adds a new outer IP header on top of the encrypted payload.
With GRE over IPsec, the GRE header already provides that outer IP header. Adding another one with IPsec tunnel mode would be redundant and waste 20 bytes per packet.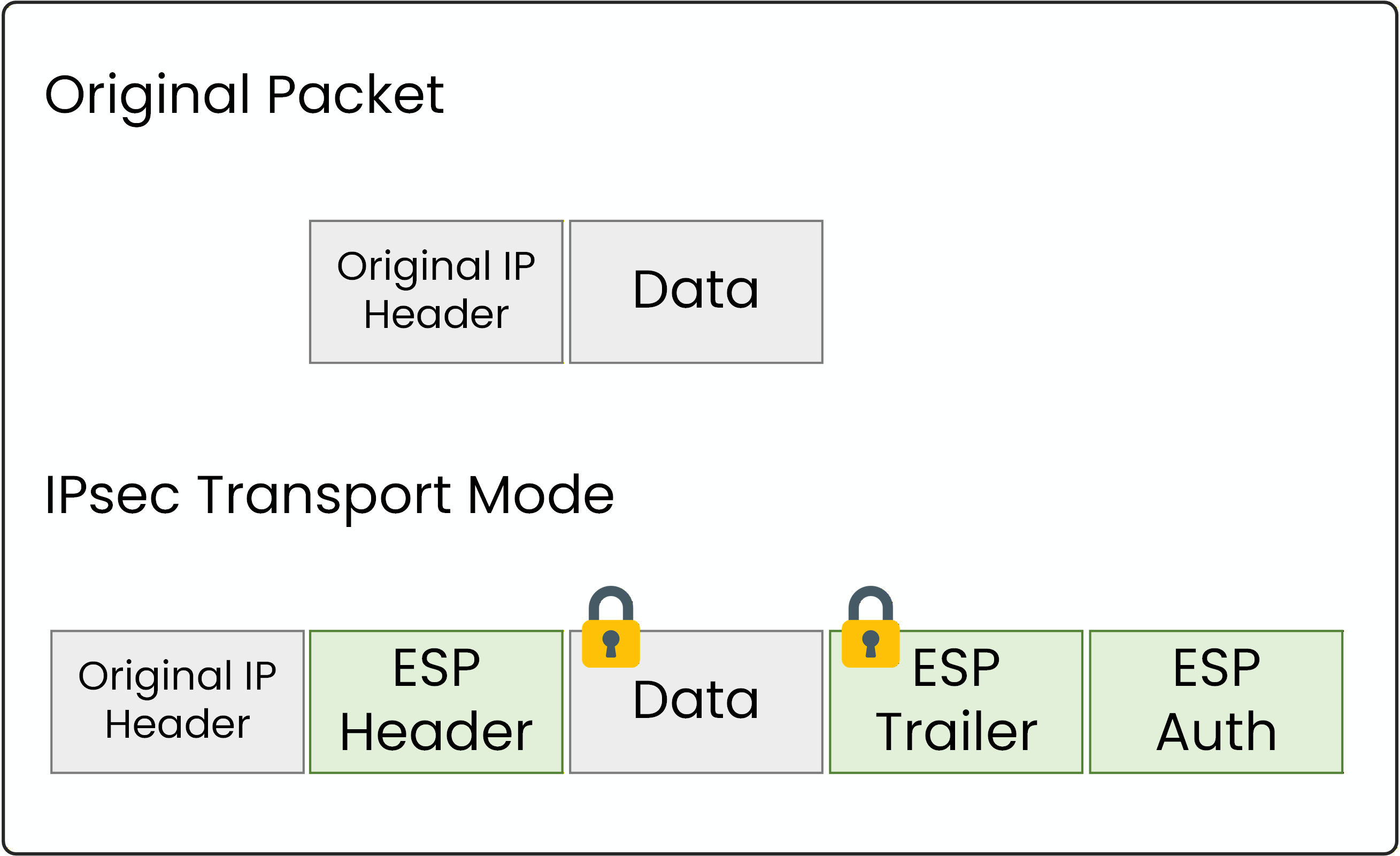
Figure 3 - IPsec transport mode
This is why you use IPsec transport mode instead.
IPsec encrypts only the payload. The GRE outer IP header handles routing across the Internet.Answer the question below
What type of traffic can IPsec not carry natively, making GRE necessary?
As the network engineer responsible for the New York (R1) and San Francisco (R2) sites, your task will be to configure the GRE over IPsec tunnel between them.
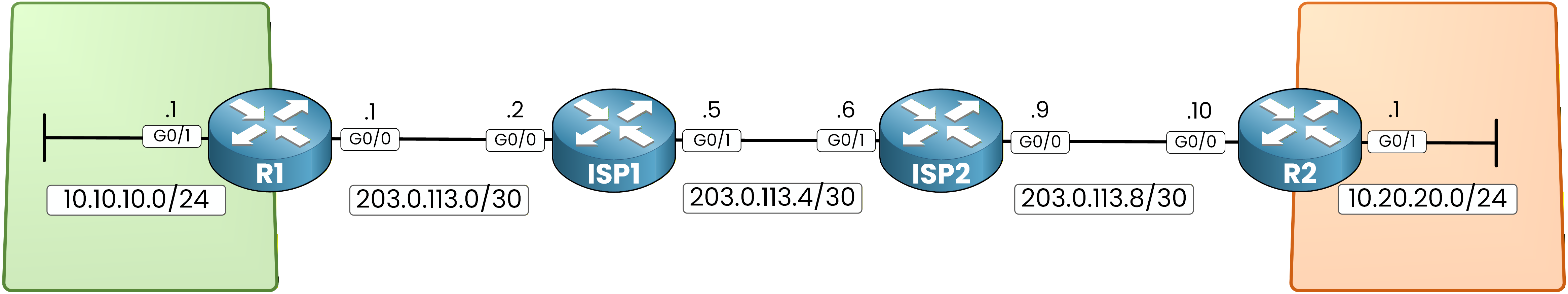
Figure 4 - GRE over IPsec lab topology
Underlay Routing
Before building the GRE tunnel, the underlay must be working.
Configure static routes on ISP1 and ISP2 so they can forward traffic between the two enterprise WAN interfaces.ISP1# conf t Enter configuration commands, one per line. End with CNTL/Z. ISP1(config)# ip route 10.10.10.0 255.255.255.0 203.0.113.1 ISP1(config)# ip route 10.20.20.0 255.255.255.0 203.0.113.6 ISP1(config)# ip route 203.0.113.8 255.255.255.252 203.0.113.6ISP2# conf t Enter configuration commands, one per line. End with CNTL/Z. ISP2(config)# ip route 10.10.10.0 255.255.255.0 203.0.113.5 ISP2(config)# ip route 10.20.20.0 255.255.255.0 203.0.113.10 ISP2(config)# ip route 203.0.113.0 255.255.255.252 203.0.113.5Each enterprise router also needs a default route toward its ISP.
R1(config)# ip route 0.0.0.0 0.0.0.0 203.0.113.2R2(config)# ip route 0.0.0.0 0.0.0.0 203.0.113.9GRE Tunnel
Your underlay is ready. Now build the GRE tunnel.
The tunnel endpoints are the WAN addresses and the tunnel uses the 192.168.100.0/30 subnet.On R1:
R1(config)# int tunnel0 %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to down R1(config-if)# ip address 192.168.100.1 255.255.255.252 R1(config-if)# tunnel source 203.0.113.1 R1(config-if)# tunnel destination 203.0.113.10 %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to up R1(config-if)# endOn R2:
R2(config)# int tunnel0 %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to down R2(config-if)# ip address 192.168.100.2 255.255.255.252 R2(config-if)# tunnel source 203.0.113.10 R2(config-if)# tunnel destination 203.0.113.1 %LINEPROTO-5-UPDOWN: Line protocol on Interface Tunnel0, changed state to up %OSPF-5-ADJCHG: Process 1, Nbr 1.1.1.1 on Tunnel0 from LOADING to FULL, Loading Done R2(config-if)# endOSPF over GRE
The tunnel is up on both routers. The OSPF adjacency message on R2 confirms Hello packets are already flowing through GRE.
Now configure OSPF across the tunnel.R1(config)# router ospf 1 R1(config-router)# router-id 1.1.1.1 R1(config-router)# network 10.10.10.0 0.0.0.255 area 0 R1(config-router)# network 192.168.100.0 0.0.0.3 area 0 R1(config-router)# exitR2(config)# router ospf 1 R2(config-router)# router-id 2.2.2.2 R2(config-router)# network 10.20.20.0 0.0.0.255 area 0 R2(config-router)# network 192.168.100.0 0.0.0.3 area 0 R2(config-router)# exitYour GRE tunnel is up and OSPF is running through it.
But traffic is still in cleartext. Now add IPsec on top to encrypt it.40 % Complete: you’re making great progress
Unlock the rest of this lesson
If you’d like to continue your CCNA journey, simply create your free account.
Access all CCNA lessons
Practice with hands-on labs
Train with Practice exams and Quizzes
Progress tracking in your dashboard
Made by network engineers - CCNP certified
learners globally